'I didn't give permission': Do AI's backers care about data law breaches? | Artificial intelligence (AI) | The Guardian

IndySoft Corporation on X: "It's the last day of Cybersecurity Awareness Month! Our final tip is regarding how to protect data on your devices if they are lost, stolen, or misplaced. #CyberSecurityAwarenessMonth #
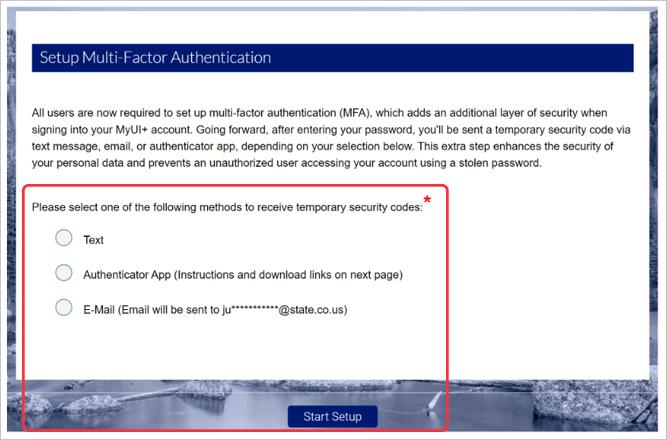
How to Register a New Third Party Administrator (TPA) Account in MyUI Employer+ | Department of Labor & Employment

I have email account on grodno.net. Now google banned the workspace. How can I restore history? - Google Workspace Admin Community